
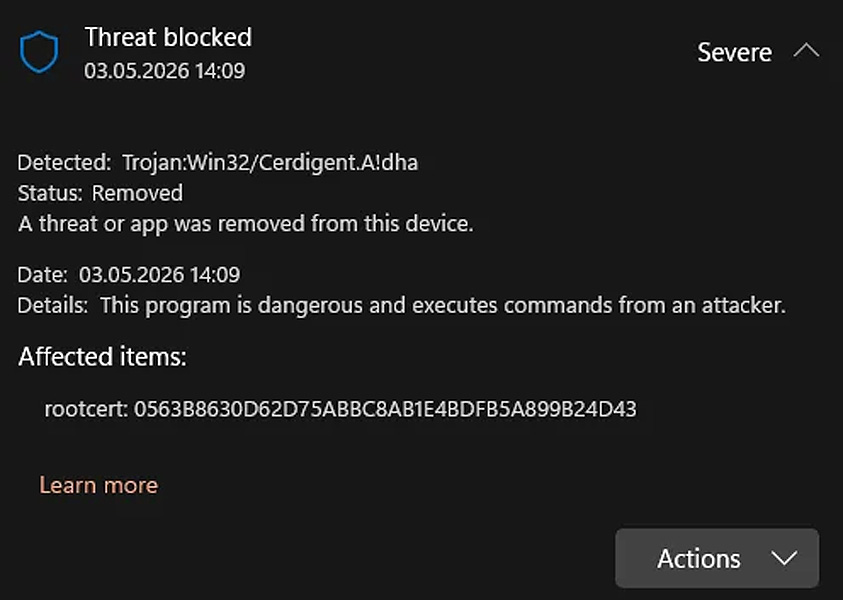
Microsoft Defender is detecting reputable DigiCert root certificates as Trojan:Win32/Cerdigent.A!dha, leading to widespread false-positive alerts, and in some circumstances, eradicating certificates from Home windows.
In keeping with cybersecurity skilled Florian Roth, the difficulty first appeared after Microsoft added the detections to a Defender signature replace on April thirtieth.
At the moment, directors worldwide started reporting that DigiCert root certificates entries had been flagged as malware and, on affected techniques, faraway from the Home windows belief retailer.
In keeping with a Reddit put up concerning the false positives, the detected certificates are:
- 0563B8630D62D75ABBC8AB1E4BDFB5A899B24D43
- DDFB16CD4931C973A2037D3FC83A4D7D775D05E4
On impacted techniques, these certificates had been faraway from the AuthRoot retailer underneath this Registry key:
HKLMSOFTWAREMicrosoftSystemCertificatesAuthRootCertificates
These false positives have led to concern amongst Home windows customers, with some considering their units had been contaminated and reinstalling the working system to be protected.
Supply: Reddit
Microsoft has reportedly mounted the detections in Safety Intelligence replace model 1.449.430.0, and the latest replace is now 1.449.431.0.
Different experiences on Reddit point out that the repair additionally restores beforehand eliminated certificates on affected techniques.
The brand new Microsoft Defender updates will routinely set up, and Home windows customers can manually power an replace by going into Home windows Safety > Virus and risk safety > Safety updates and clicking on Examine for Updates.
Presumably linked to a current DigiCert breach
The false positives happen shortly after a disclosed DigiCert safety incident that enabled risk actors to acquire legitimate code-signing certificates used to signal malware.
“A malware incident focused a buyer help staff member. Upon detection, the risk vector was contained,” explains the DigiCert incident report.
“Our subsequent investigation discovered that the risk actor was in a position to procure initialization codes for a restricted variety of code signing certificates, few of which had been then used to signal malware.”
“The recognized certificates had been revoked inside 24 hours of discovery and the revocation date set to their date of issuance. As a precautionary measure, pending orders throughout the window of curiosity had been cancelled. Extra particulars shall be supplied in our full incident report.”
In keeping with DigiCert’s incident report, attackers focused the corporate’s help employees in early April by creating help messages containing a malicious ZIP file disguised as a screenshot.
After a number of blocked makes an attempt, one help analyst’s machine was finally compromised, adopted by a second system that went undetected for a time as a result of an endpoint safety “sensor hole.”
Utilizing entry to the breached help surroundings, the hacker used a characteristic in DigiCert’s inside help portal that allowed help employees to view buyer accounts from the client’s perspective.
Whereas restricted in scope, this entry uncovered “initialization codes” to beforehand permitted, however undelivered, EV code-signing certificates orders.
“Possession of an initialization code, mixed with an permitted order, is enough to acquire the ensuing certificates (see Contributing Components dialogue beneath),” defined DigiCert.
“For the reason that risk actor was in a position to receive these two items of knowledge for a finite set of permitted orders, they had been in a position to receive EV Code Signing certificates throughout a set of buyer accounts and CAs.”
DigiCert says it revoked 60 code-signing certificates, together with 27 linked to a “Zhong Stealer” malware marketing campaign.
“11 had been recognized in certificates drawback experiences supplied to DigiCert by neighborhood members linking the certificates to malware, and 16 had been recognized throughout our personal investigation,” defined DigiCert.
Zhong Stealer malware marketing campaign
This aligns with earlier experiences from safety researchers who had noticed newly issued DigiCert EV certificates utilized in malware campaigns and reported them to DigiCert.
Researchers, together with Squiblydoo, MalwareHunterTeam, and g0njxa, reported that certificates issued to well-known corporations equivalent to Lenovo, Kingston, Shuttle Inc, and Palit Microsystems had been getting used to signal malware.
“What do Lenovo, Kingston, Shuttle Inc, and Palit Microsystems have in widespread?,” posted Squiblydoo on X.
“EV Certificates from these corporations had been issued and utilized by a Chinese language crime group, #GoldenEyeDog (#APT-Q-27)!”
The malware on this marketing campaign is called “Zhong Stealer,” although evaluation signifies it could be extra like a distant entry trojan (RAT) than an infostealer.
The researcher says the malware was distributed by the next assaults:
- Phishing emails ship a pretend picture or screenshot
- A primary-stage executable that shows a decoy picture
- Retrieval of a second-stage payload from cloud storage equivalent to AWS
- Use of signed binaries and loaders, together with elements tied to reputable distributors
After DigiCert disclosed the incident, the researchers mentioned the incident report explains how the certificates utilized in these malware campaigns had been obtained.
Whereas Microsoft has not confirmed that the Defender detections are a results of the DigiCert incident, the timing and deal with DigiCert-related certificates counsel a doable connection.
Nevertheless, it needs to be famous that the certificates flagged by Microsoft Defender are root certificates within the Home windows belief retailer and don’t match the revoked DigiCert code-signing certificates used to signal malware.
BleepingComputer contacted Microsoft with questions concerning the marketing campaign, together with whether or not it was tied to DigiCert’s breach.
AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of recent exploits is coming.
On the Autonomous Validation Summit (Might 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls maintain, and closes the remediation loop.


