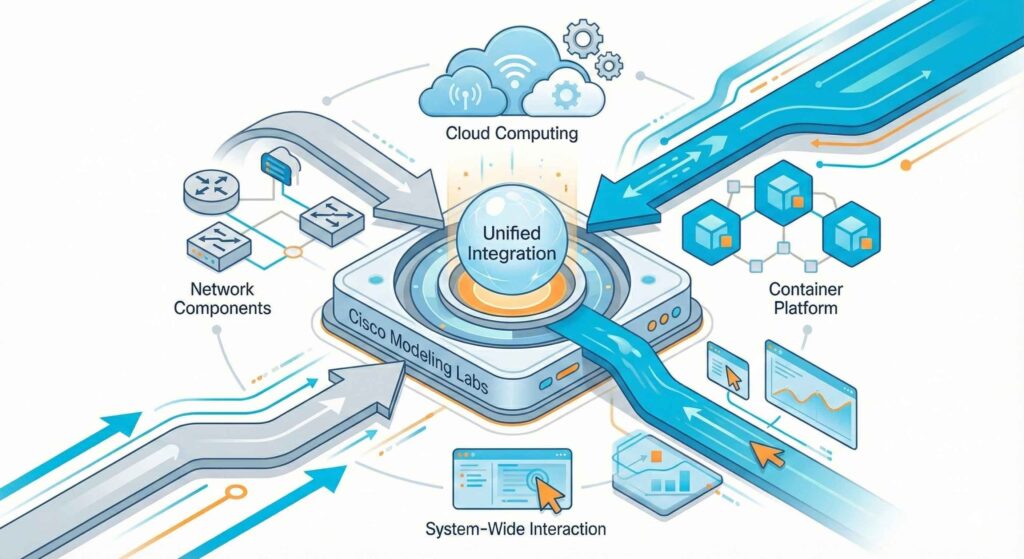
Container nodes in Cisco Modeling Labs (CML) 2.9 complement digital machines, providing higher flexibility and effectivity. Engineers profit from having light-weight, programmable, and quickly deployable choices inside their simulation environments. Whereas digital machines (VMs) dominate with community working programs, containers add flexibility, enabling instruments, visitors injectors, automation, and full functions to run easily together with your CML topology. Conventional digital machines are nonetheless efficient, however customized containers introduce a transformative agility.
Constructing photographs that behave predictably and combine cleanly with simulated networks is way simpler with containers. As anybody who has tried to drop a inventory Docker picture into CML shortly discovers, this isn’t an easy course of. Typical Docker photographs lack the mandatory CML-compatible metadata, community interface behaviors, and lifecycle properties. Utilizing containers with CML is the lacking factor.
This weblog put up supplies a sensible, engineering-first walkthrough for constructing containers which might be actually CML-ready.
Word about enhancements to CML: When containers have been launched, just one picture per node definition was allowed. With the CML 2.10 launch, this restriction has been lifted. Particularly, the next enhancements will likely be added:
- Per picture definition, Docker tag names reminiscent of:
debian:bookworm, debian:buster and debian:trixie
Are all legitimate tags for a similar “debian-docker” node definitions—three legitimate picture definitions for one node definition.
- Specification of Docker tags as a substitute for picture names (.tar.gz information) and SHA256 has sums. On this case, CML will attempt to obtain the picture from a container registry, e.g., Docker Hub, if not in any other case specified.
- Improved launch logic to keep away from “perpetual launches” in case the SHA256 sum from the picture definition didn’t match the precise hash sum within the picture.
Why do customized containers in CML matter?
Conventional CML workflows depend on VM-based nodes operating IOSv, IOS-XRv, NX-OS, Ubuntu, Alpine, and different working programs. These are wonderful for modeling community working system habits, however they’re heavyweight for duties reminiscent of integrating CLI instruments, internet browsers, ephemeral controllers, containerized apps, microservices, and testing harnesses into your simulations.
Containers begin shortly, eat fewer assets, and combine easily with customary NetDevOps CI/CD workflows. Regardless of their benefits, integrating customary Docker photographs into CML isn’t with out its challenges, every of which requires a tailor-made resolution for seamless performance.
The hidden challenges: why a Docker picture isn’t sufficient
CML doesn’t run containers in the identical approach a vanilla Docker Engine does. As a substitute, it wraps containers in a specialised runtime surroundings that integrates with its simulation engine. This results in a number of potential pitfalls:
- Entry factors and init programs
Many base photographs assume they’re the solely course of operating. In CML, community interfaces, startup scripts, and boot readiness needs to be supplied. Additionally, CML expects a long-running foreground course of. In case your container exits instantly, CML will deal with the node as “failed.” - Interface mapping
Containers typically use eth0, but CML attaches interfaces sequentially primarily based on topology (eth0, eth1, eth2…). Your picture ought to deal with extra interfaces added at startup, mapping them to particular OS configurations. - Capabilities and customers
Some containers drop privileges by default. CML’s bootstrap course of may have particular entry privileges to configure networking or begin daemons. - Filesystem format
CML makes use of non-obligatory bootstrap property injected into the container’s filesystem. A typical Docker picture received’t have the suitable directories, binaries, or permissions for this. If wanted, CML can “inject” a full suite of command-line binaries (“busybox”) right into a container to offer a correct CLI surroundings. - Lifecycle expectations
Containers ought to output log data to the console in order that performance could be noticed in CML. For instance, an online server ought to present the entry log.
Misalign any of those, and also you’ll spend hours troubleshooting what seems to be a easy “it really works with run” situation.
How CML treats containers: A psychological mannequin for engineers
CML’s container capabilities revolve round a node-definition YAML file that describes:
- The picture to load or pull
- The bootstrap course of
- Setting variables
- Interfaces and the way they bind
- Simulation habits (startup order, CPU/reminiscence, logging)
- UI metadata
When a lab launches, CML:
- Deploys a container node
- Pulls or masses the container picture
- Applies networking definitions
- Injects metadata, IP deal with, and bootstrap scripts
- Screens node well being through logs and runtime state
Consider CML as “Docker-with-constraints-plus-network-injection.” Understanding CML’s method to containers is foundational, however constructing them requires specifics—listed below are sensible suggestions to make sure your containers are CML-ready.
Ideas for constructing a CML-ready container
The container photographs constructed for CML 2.10 and ahead are created on GitHub. We use a GitHub Motion CI workflow to completely automate the construct course of. You possibly can, in actual fact, use the identical workflow to construct your personal customized photographs able to be deployed in CML. There’s loads of documentation and examples that you could construct off of, supplied within the repository* and on the Deep Wiki.**
Necessary word: CML treats every node in a topology as a single, self-contained service or software. Whereas it may be tempting to instantly deploy multi-container functions, typically outlined utilizing docker-compose , into CML by trying to separate them into particular person CML nodes, this method is usually not advisable and might result in vital problems.
1.) Select the suitable base
Begin from an already current container definition, like:
- nginx (single-purpose community daemon utilizing a vanilla upstream picture).
- Firefox (graphical consumer interface, customized construct course of).
- Or a customized CI-built base together with your customary automation framework.
Keep away from utilizing photographs that depend on SystemD until you explicitly configure it; SystemD inside containers could be tough.
2.) Outline a correct entry level
Your container should:
- Run a long-lived course of.
- Not daemonize within the background.
- Assist predictable logging.
- Preserve the container “alive” for CML.
Right here’s a easy supervisor script:
#!bin/sh echo "Container beginning..." tail -f /dev/null
Not glamorous, however efficient. You possibly can substitute tail -f /dev/null together with your service startup chain.
3.) Put together for a number of interfaces
CML might connect a number of interfaces to your topology. CML will run a DHCP course of on the primary interface, however until that first interface is L2-adjacent to an exterior connector in NAT mode, there’s NO assure it’s going to purchase one! If it can’t purchase an IP deal with, it’s the lab admin’s accountability to offer IP deal with configuration per the day 0 configuration. Usually, ip config … instructions can be utilized for this goal.
Superior use instances you’ll be able to unlock
When you conquer customized containers, CML turns into dramatically extra versatile. Some in style use instances amongst superior NetDevOps and SRE groups embrace:
Artificial visitors and testing
Automation engines
- Nornir nodes
- pyATS/Genie take a look at harness containers
- Ansible automation controllers
Distributed functions
- Primary service-mesh experiments
- API gateways and proxies
- Container-based middleboxes
Safety instruments
- Honeypots
- IDS/IPS elements
- Packet inspection frameworks
Deal with CML as a “full-stack lab,” enhancing its capabilities past a mere community simulator.
Make CML your personal lab
Creating customized containers for CML turns the platform from a simulation device into a whole, programmable take a look at surroundings. Whether or not you’re validating automation workflows, modeling distributed programs, prototyping community capabilities, or just constructing light-weight utilities, containerized nodes mean you can adapt CML to your engineering wants—not the opposite approach round.
In the event you’re prepared to increase your CML lab, the easiest way to begin is easy: construct a small container, copy and modify an current node definition, and drop it right into a two-node topology. When you see how easily it really works, you’ll shortly notice simply how far you’ll be able to push this function.
Would you wish to make your personal customized container for CML? Tell us within the feedback!
* Github Repository – Automation for constructing CML Docker Containers
** DeepWiki – CML Docker Containers (CML 2.9+)
Join Cisco U. | Be part of the Cisco Studying Community at the moment free of charge.
Observe Study with Cisco
X | Threads | Fb | LinkedIn | Instagram | YouTube
Use #CiscoU and #CiscoCert to hitch the dialog.

