
A brand new marketing campaign delivering the Atomic Stealer malware to macOS customers abuses the Script Editor in a variation of the ClickFix assault that tricked customers into executing instructions in Terminal.
Script Editor is a built-in macOS utility for writing and working scripts, primarily AppleScript and JXA, that may execute native scripts and shell instructions. It’s a trusted utility pre-installed on macOS methods.
Whereas this isn’t the primary time it has been abused for malware supply, the researchers be aware that, within the context of the ClickFix social engineering method, it doesn’t require the sufferer to manually work together with the Terminal and execute instructions.
Aside from the Terminal-based variant being extensively reported, macOS Tahoe 26.4 added safety towards ClickFix assaults within the type of a warning when attempting to execute instructions.
In a brand new marketing campaign distributing Atomic Stealer noticed by safety researchers at Jamf, the hackers goal victims with faux Apple-themed websites that pose as guides to assist reclaim disk area on their Mac computer systems.
These pages include legitimate-looking system cleanup directions however use the applescript:// URL scheme to launch Script Editor with a pre-filled executable code.
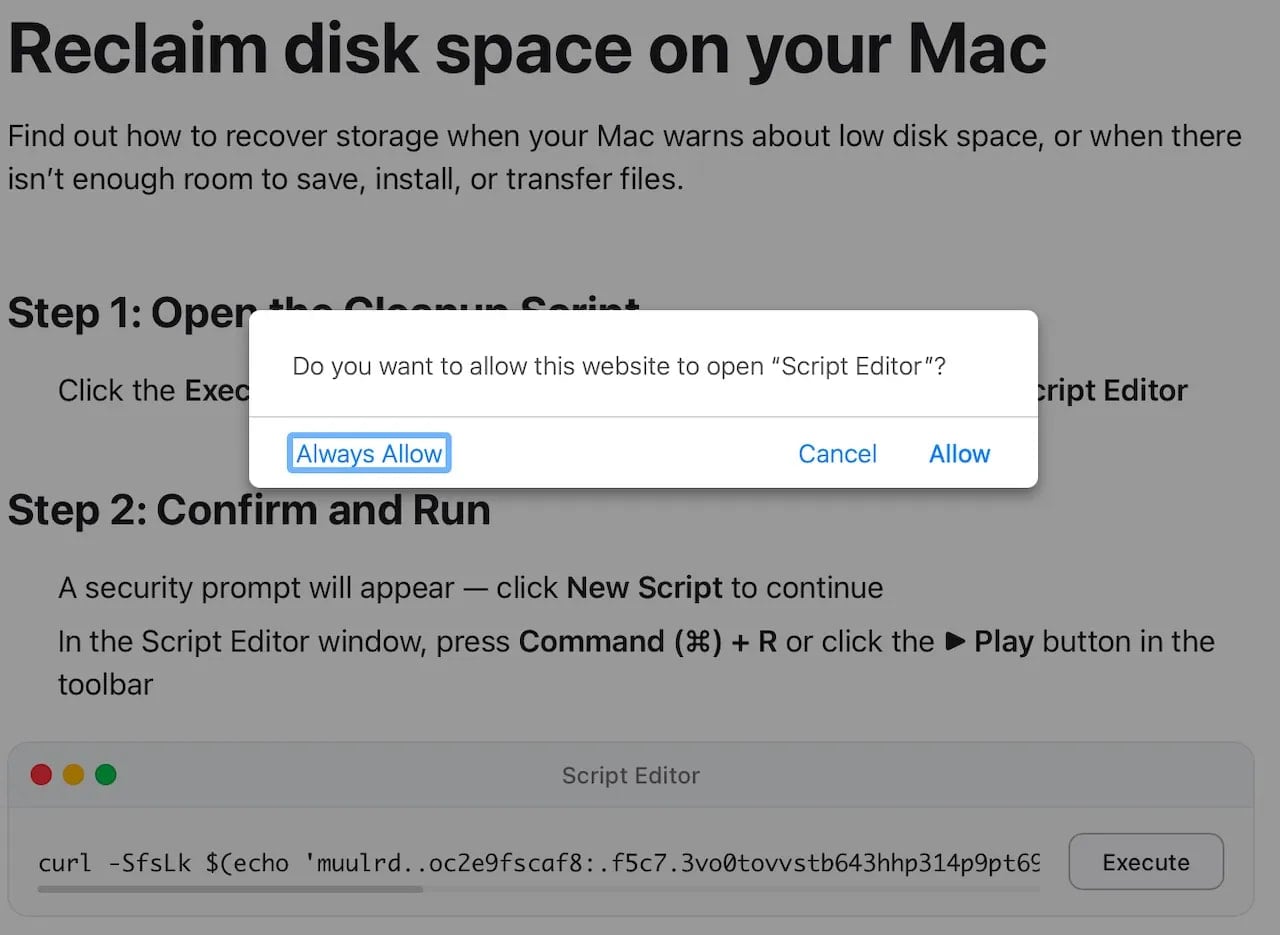
Supply: Jamf
The malicious code runs an obfuscated ‘curl | zsh’ command, which downloads and executes a script instantly in system reminiscence.
This decodes a base64 + gzip payload, downloads a binary (/tmp/helper), removes safety attributes by way of ‘xattr -c,’ makes it executable, and runs it.
The ultimate payload is a Mach-O binary recognized as Atomic Stealer (AMOS), a commodity malware-as-a-service that has been extensively deployed in ClickFix campaigns utilizing varied lures over the previous 12 months.
The malware targets a broad spectrum of delicate information, together with info saved within the Keychain, desktop, and browser cryptocurrency pockets extensions, browser autofill information, passwords, cookies, saved bank cards, and system info.
Final 12 months, AMOS additionally added a backdoor element to present operators persistent entry to compromised methods.
Mac customers ought to deal with Script Editor prompts as high-risk and keep away from working them on their units until they absolutely perceive what they do and belief the useful resource.
For macOS troubleshooting guides, it is suggested to rely solely on official documentation from Apple.
Apple Assist Communities, the discussion board the place Apple clients will help one another with recommendation, though it will not be risk-free.
Automated pentesting proves the trail exists. BAS proves whether or not your controls cease it. Most groups run one with out the opposite.
This whitepaper maps six validation surfaces, reveals the place protection ends, and supplies practitioners with three diagnostic questions for any software analysis.



