
A China-linked superior persistent menace actor tracked as UAT-9244 has been concentrating on telecommunication service suppliers in South America since 2024, compromising Home windows, Linux, and network-edge gadgets.
In accordance with Cisco Talos researchers, the adversary is intently related to the FamousSparrow and Tropic Trooper hacker teams, however is tracked as a separate exercise cluster.
This evaluation has excessive confidence and is predicated on comparable tooling, ways, methods, and procedures (TTPs), and victimology noticed in assaults attributed to the menace actors.
The researchers notice that whereas UAT-9244 shares the identical goal profile as Salt Hurricane, they may not set up a strong connection between the 2 exercise clusters.
New malware concentrating on telco networks
The researchers discovered that the marketing campaign used three beforehand undocumented malware households: TernDoor, a Home windows backdoor; PeerTime, a Linux backdoor that makes use of BitTorrent; and BruteEntry, a brute-force scanner that builds proxy infrastructure (ORBs).
TernDoor is deployed by means of DLL side-loading, utilizing the respectable executable wsprint.exe to load malicious code from BugSplatRc64.dll, which decrypts and executes the ultimate payload in reminiscence (injected into msiexec.exe).
The malware incorporates an embedded Home windows driver, WSPrint.sys, which is used to terminate, droop, and resume processes.
Persistence is achieved by way of scheduled duties and Home windows Registry modifications, that are additionally used to cover the scheduled process.
Moreover, TernDoor can execute instructions by way of distant shell, run arbitrary processes, learn/write information, accumulate system info, and self-uninstall.
PeerTime is an ELF Linux backdoor that targets a number of architectures (ARM, AARCH, PPC, MIPS), suggesting it was designed to compromise a broad vary of embedded techniques and community gadgets utilized in telecom environments.

Supply: Cisco Talos
Cisco Talos documented two variations for PeerTime. One variant is written in C/C++ and the opposite is predicated on Rust. The researchers additionally seen Simplified Chinese language debug strings within the instrumentor binary, an indicator of its origin.
Its payload is decrypted and loaded in reminiscence, and its course of is renamed to seem respectable.
PeerTime, an ELF-based peer-to-peer (P2P) backdoor, makes use of the BitTorrent protocol for command-and-control (C2) communications, downloads and executes payloads from friends, and makes use of BusyBox to put in writing the information on the host.
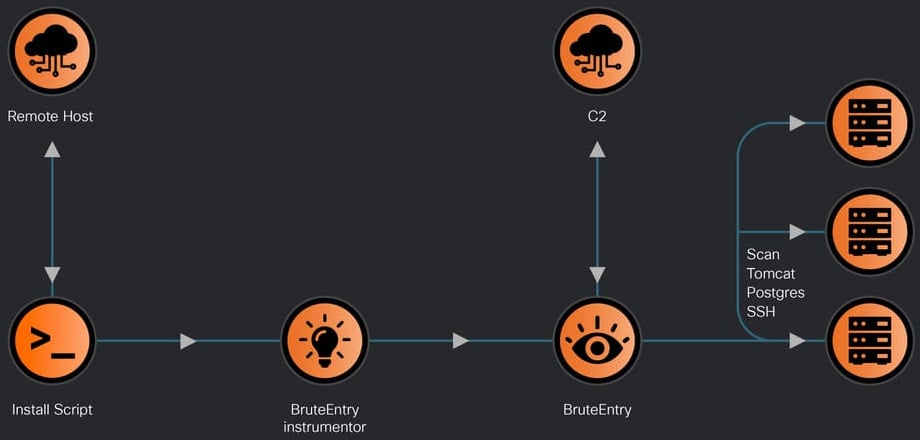
Lastly, there’s BruteEntry, which consists of a Go-based instrumentor binary and a brute-forcing part. Its position is to show compromised gadgets into scanning nodes, referred to as Operational Relay Containers (ORBs).
Supply: Cisco Talos
The attacker makes use of the machines working BruteEntry to scan for brand new targets and brute-force entry to SSH, Postgres, and Tomcat. Login try outcomes are despatched again to the C2 with process standing and notes.
In a technical report at present, Cisco Talos researchers present particulars on the capabilities of the three items of malware, how they’re deployed, and obtain persistence.
Cisco Talos researchers have listed indicators of compromise (IoCs) related to the noticed UAT-9244 exercise, which defenders can use to detect and block these assaults early.


