A remarkably widespread case in giant established enterprises is that there
are programs that no person desires to the touch, however everybody is determined by. They run
payrolls, deal with logistics, reconcile stock, or course of buyer orders.
They’ve been in place and evolving slowly for many years, constructed on stacks no
one teaches anymore, and maintained by a shrinking pool of consultants. It’s
onerous to search out an individual (or a group) that may confidently say that they know
the system properly and are prepared to supply the purposeful specs. This
state of affairs results in a very lengthy cycle of research, and lots of packages get
lengthy delayed or stopped mid approach due to the Evaluation Paralysis.
These programs usually stay inside frozen environments: outdated databases,
legacy working programs, brittle VMs. Documentation is both lacking or
hopelessly out of sync with actuality. The individuals who wrote the code have lengthy
since moved on. But the enterprise logic they embody continues to be vital to
each day operations of hundreds of customers. The result’s what we name a black
field: a system whose outputs we are able to observe, however whose interior workings stay
opaque. For CXOs and know-how leaders, these black packing containers create a
modernization impasse
- Too dangerous to switch with out totally understanding them
- Too expensive to keep up on life assist
- Too vital to disregard
That is the place AI-assisted reverse engineering turns into not only a
technical curiosity, however a strategic enabler. By reconstructing the
purposeful intent of a system,even when it’s lacking the supply code, we are able to
flip worry and opacity into readability. And with readability comes the boldness to
modernize.
The System we Encountered
The system itself was huge in each scale and complexity. Its databases
throughout a number of platforms contained greater than 650 tables and 1,200 saved
procedures, reflecting many years of evolving enterprise guidelines. Performance
prolonged throughout 24 enterprise domains and was introduced by means of practically 350
consumer screens. Behind the scenes, the appliance tier consisted of 45
compiled DLLs, every with hundreds of features and nearly no surviving
documentation. This intricate mesh of information, logic, and consumer workflows,
tightly built-in with a number of enterprise programs and databases, made
the appliance extraordinarily difficult to modernize
Our process was to hold out an experiment to see if we may use AI to
create a purposeful specification of the prevailing system with enough
element to drive the implementation of a alternative system. We accomplished
the experiment section for an finish to finish skinny slice with reverse and ahead
engineering. Our confidence stage is greater than excessive as a result of we did a number of
ranges of cross checking and verification. We walked by means of the reverse
engineered purposeful spec with sys-admin / customers to substantiate the meant
performance and in addition verified that the spec we generated is enough
for ahead engineering as properly.
The consumer issued an RFP for this work, with we estimated would take 6
months for a group of peak 20 individuals. Sadly for us, they determined to work
with one in all their current most popular companions, so we cannot be capable to see
how our experiment scales to the total system in apply. We do, nonetheless,
assume we realized sufficient from the train to be value sharing with our
skilled colleagues.
Key Challenges
- Lacking Supply Code: legacy understanding is already complicated if you
have supply code and an SME (in some type) to place every part collectively. When the
supply code is lacking and there are not any consultants it’s a good larger problem.
What’s left are some compiled binaries. These will not be the current binaries that
are straightforward to decompile on account of wealthy metadata (like .NET assemblies or JARs), these
are even older binaries: the type that you simply may see in outdated home windows XP underneath
C:Home windowssystem32. Even when the database is accessible, it doesn’t inform
the entire story. Saved procedures and triggers encode many years of accrued
enterprise guidelines. Schema displays compromises made based mostly on context unknown. - Outdated Infrastructure: OS and DB reached finish of life, long gone its
LTS. Utility has been in a frozen state within the type of VM resulting in
vital threat to not solely enterprise continuity, additionally considerably rising
safety vulnerability, non compliance and threat legal responsibility. - Institutional Data Misplaced: whereas hundreds of finish customers are
repeatedly utilizing the system, there’s hardly any enterprise data out there
past the occasional assist actions. The stay system is one of the best supply of
data. The one dependable view of performance is what customers see on display.
However the UI captures solely the “final mile” of execution. Behind every display lies a
tangled internet of logic deeply built-in to a number of different core programs. This can be a
widespread problem, and this technique was no exception, having a historical past of a number of
failed makes an attempt to modernize.
Our Aim
The target is to create a wealthy, complete purposeful specification
of the legacy system without having its authentic code, however with excessive
confidence. This specification then serves because the blueprint for constructing a
trendy alternative utility from a clear slate.
- Perceive total image of the system boundary and the mixing
patterns - Construct detailed understanding of every purposeful space
- Establish the widespread and distinctive eventualities
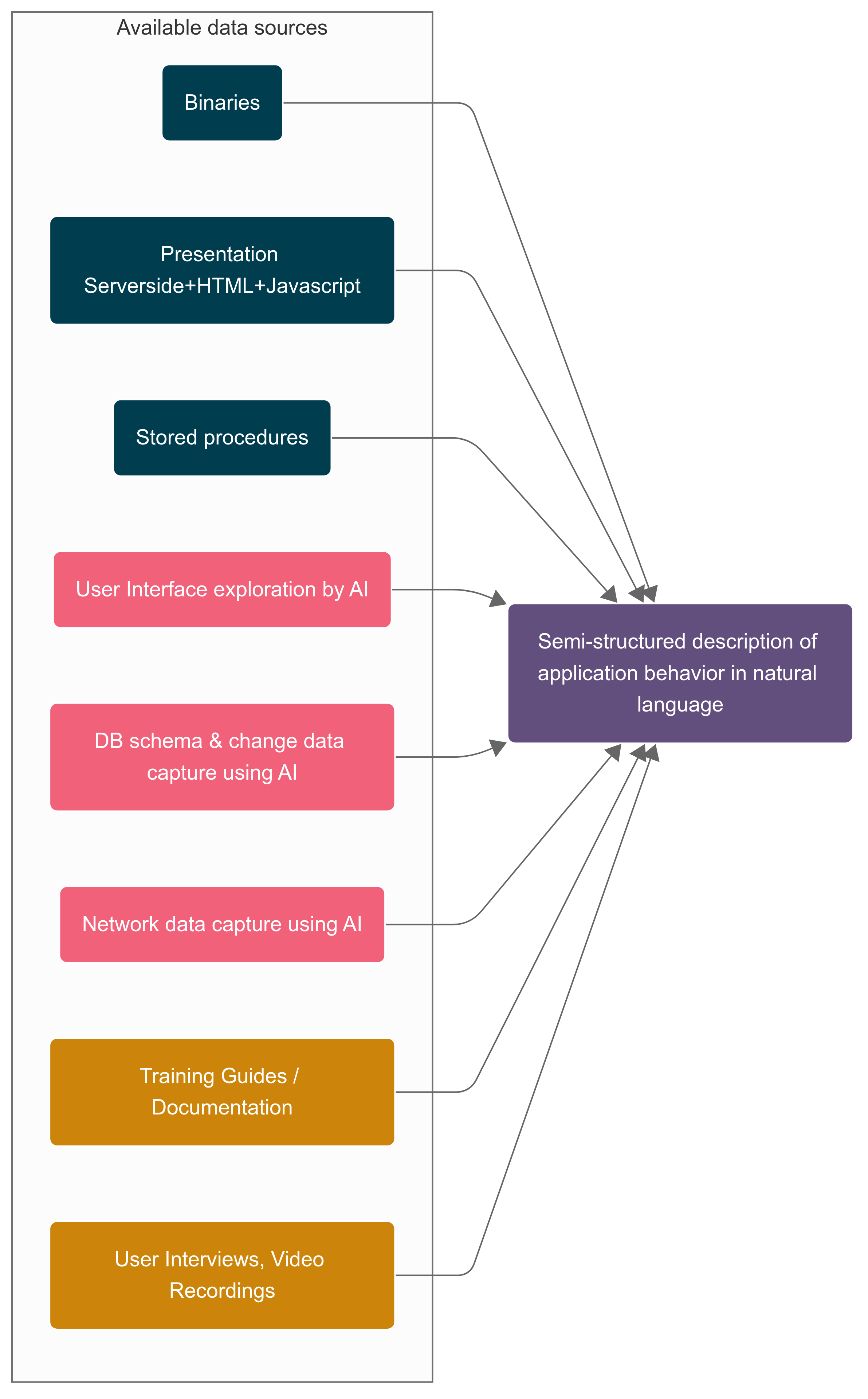
To make sense of a black-box system, we would have liked a structured option to pull
collectively fragments from totally different sources. Our precept was easy: don’t
attempt to recuperate the code — reconstruct the purposeful intent.
Our Multi Lens Method
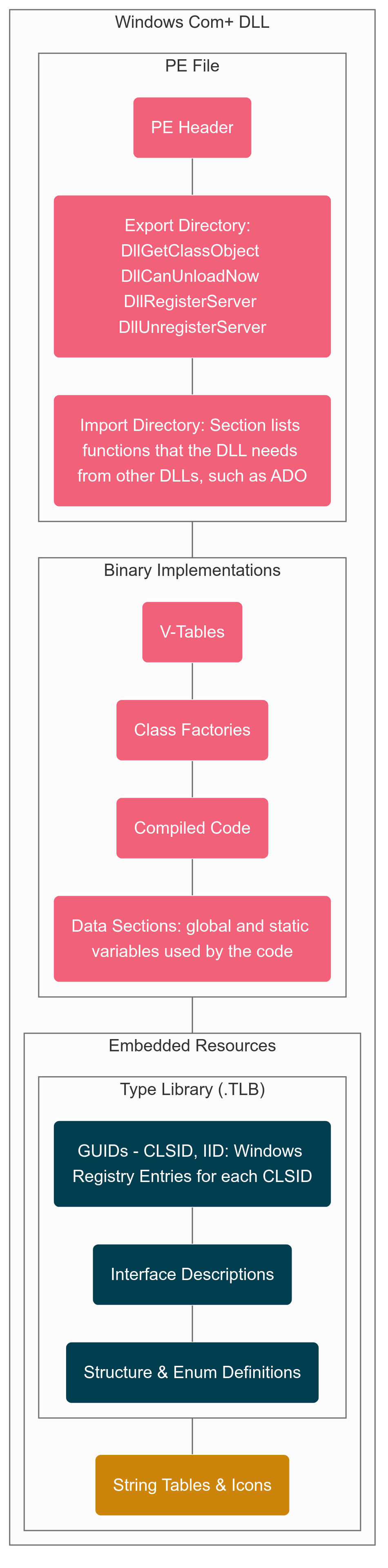
It was a 3 tier structure – Internet Tier (ASP), App Tier (DLL) and
Persistence (SQL). This structure sample gave us a leap begin even with out
supply repo. We extracted ASP recordsdata and DB schema, saved procedures from the
manufacturing system. For App Tier we solely have the native binaries. With all
this data out there, we deliberate to create a semi-structured
description of utility habits in pure language for the enterprise
customers to validate their understanding and expectations and use the validated
purposeful spec to do accelerated ahead engineering. For the semi-structured
description, our method had broadly two elements
- Utilizing AI to attach dots throughout totally different knowledge sources
- AI assisted binary Archaeology to uncover the hidden performance from
the native DLL recordsdata
Join dots throughout totally different knowledge sources
UI Layer Reconstruction
Shopping the prevailing stay utility and screenshots, we recognized the
UI components. Utilizing the ASP and JS content material the dynamic behaviour related
with the UI component may very well be added. This gave us a UI spec like under:
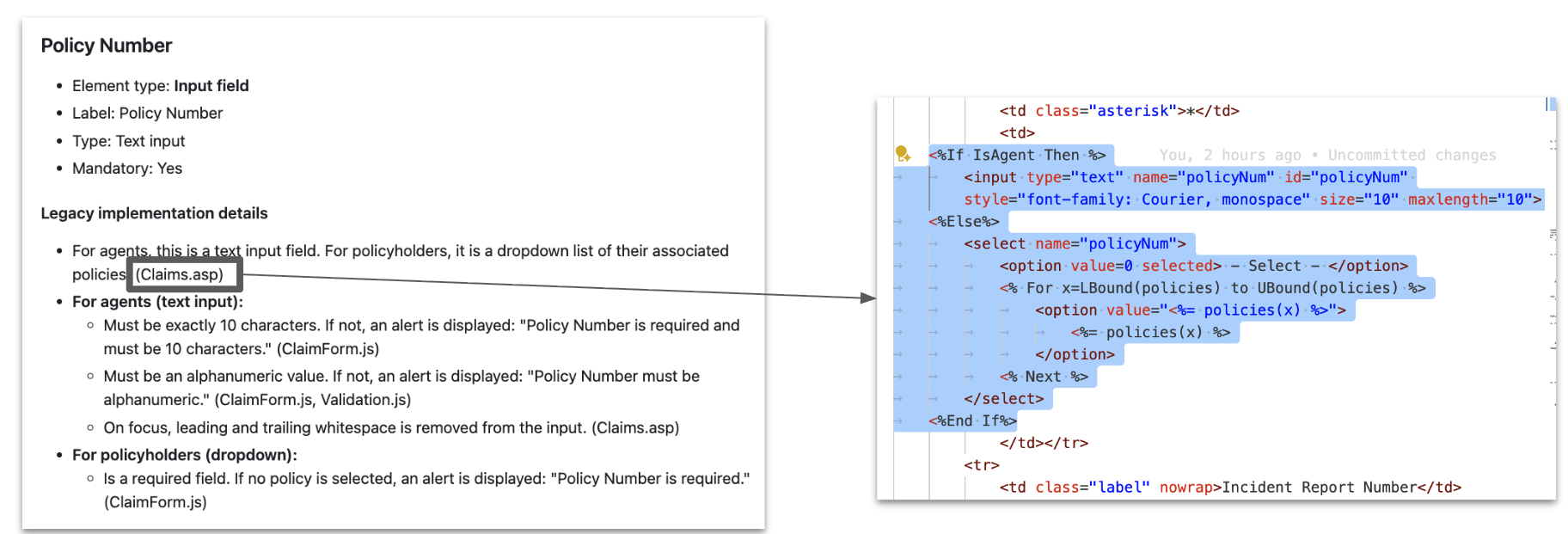
What we regarded for: validation guidelines, navigation paths, hidden fields. One
of the important thing challenges we confronted from the early stage was hallucination, each
step we added an in depth lineage to make sure that we cross verify and make sure. In
the above instance we had the lineage of the place it comes from. Following this
sample, for each key data we added the lineage together with the
context. Right here the LLM actually sped up the summarizing of huge numbers of
display definitions and consolidating logic from ASP and JS sources with the
already recognized UI layouts and subject descriptions that might in any other case take
weeks to create and consolidate.
Discovery with Change Information Seize (CDC)
We deliberate to make use of Change Information Seize (CDC) to hint how UI actions mapped
to database exercise, retrieving change logs from MCP servers to trace the
workflows. Setting constraints meant CDC may solely be enabled partially,
limiting the breadth of captured knowledge.
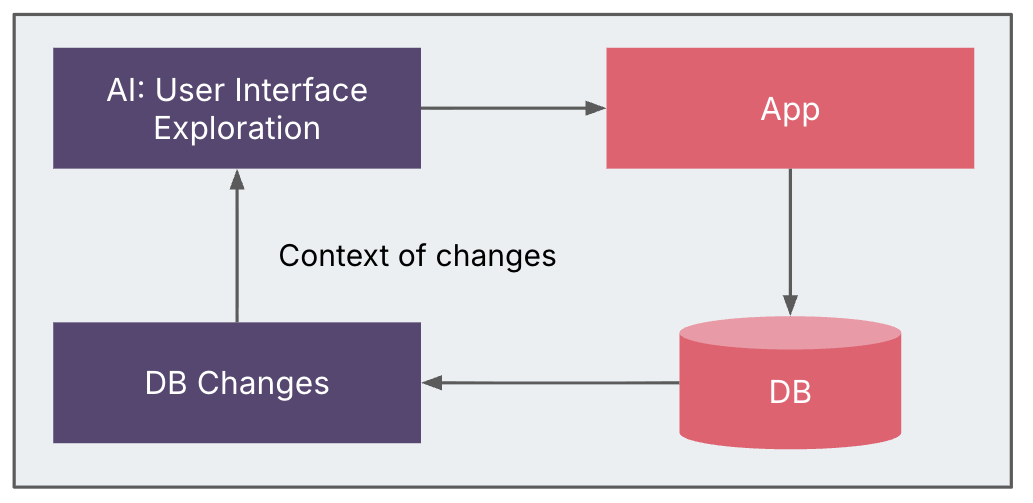
Different potential sources—comparable to front-end/back-end community site visitors,
filesystem adjustments, extra persistence layers, and even debugging
breakpoints—stay viable choices for finer-grained discovery. Even with
partial CDC, the insights proved helpful in linking UI habits to underlying
knowledge adjustments and enriching the system blueprint.
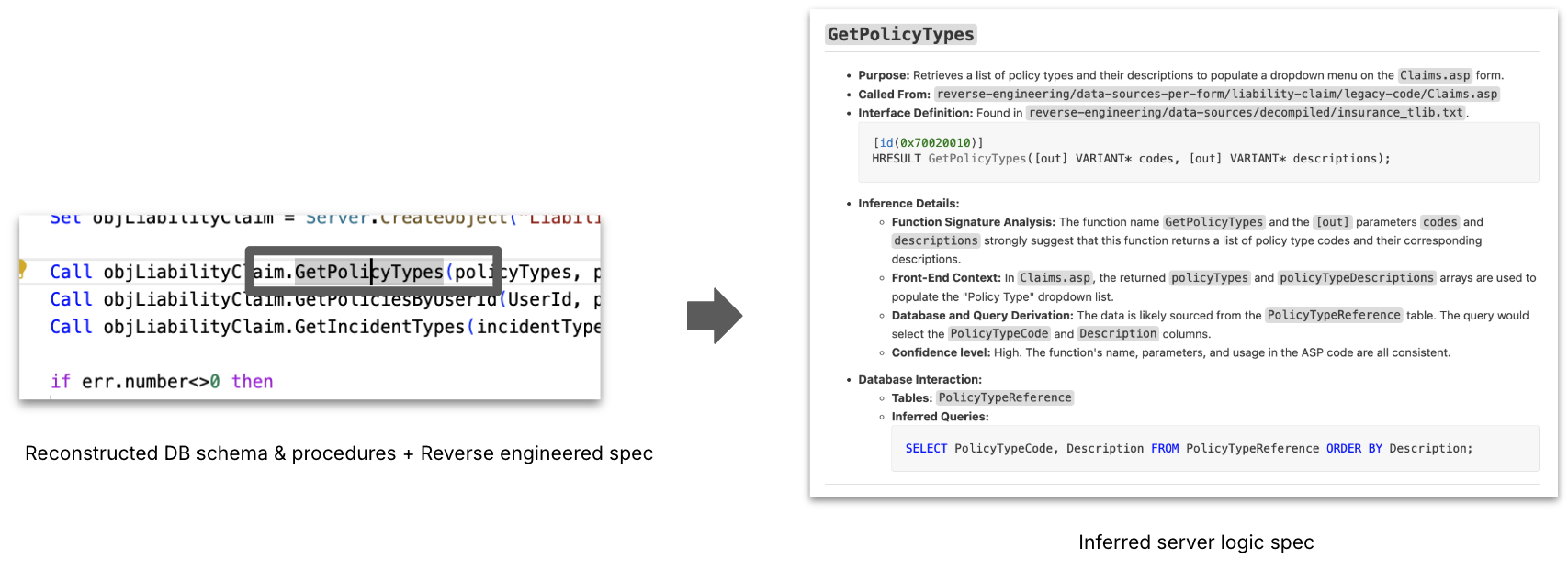
Server Logic Inferance
We then added extra context by supplying
typelibs that had been extracted from the native binaries, and saved procedures,
and schema extracted from the database. At this level with details about
format, presentation logic, and DB adjustments, the server logic will be inferred,
which saved procedures are possible referred to as, and which tables are concerned for
most strategies and interfaces outlined within the native binaries. This course of leads
to an Inferred Server Logic Spec. LLM helped in proposing possible relationships
between App tier code and procedures / tables, which we then validated by means of
noticed knowledge flows.
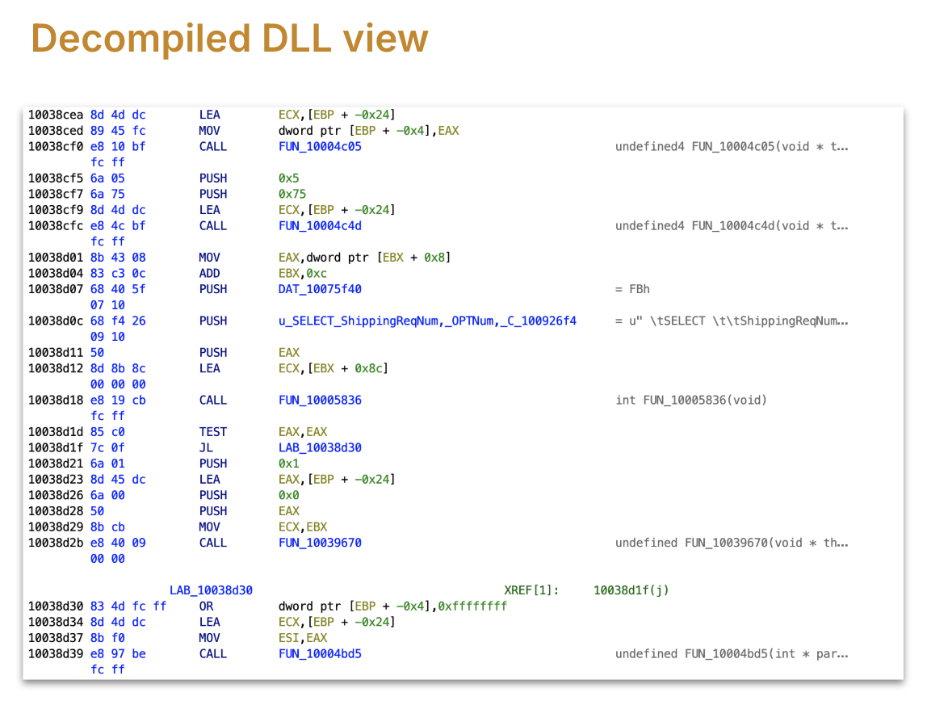
AI assisted Binary Archaeology
Essentially the most opaque layer was the compiled binaries (DLLs, executables). Right here,
we handled binaries as artifacts to be decoded quite than rebuilt. What we
regarded for: name bushes, recurring meeting patterns, candidate entry factors.
AI assisted in bulk summarizing disassembled code into human-readable
hypotheses, flagging possible operate roles — all the time validated by human
consultants.
The impression of not having good deployment practices was evident with the
Manufacturing machine having a number of variations of the identical file with file names
used to determine totally different variations and complicated names. Timestamps offered
some clues. Finding the binaries was additionally performed utilizing the home windows registry.
There have been additionally proxies for every binary that handed calls to the precise binary
to permit the App tier to run on a unique machine than the net tier. The
incontrovertible fact that proxy binaries had the identical identify as goal binaries provides to
confusion.
We did not have to take a look at binary code of DLL. Instruments like Ghidra assist to
decompile binary to an enormous set of ASM features. A few of these instruments even have
the choice to transform ASM into C code however we discovered that conversions will not be
all the time correct. In our case decompilation to C missed an important lead.
Every DLL had 1000s of meeting features, and we settled on an method
the place we determine the related features for a purposeful space and decode what
that subtree of related features does.
Prior Makes an attempt
Earlier than we arrived at this method, we tried
- brute-force technique: Added all meeting features right into a workspace, and used
the LLM agent to make it humanly readable pseudocode. Confronted a number of challenges
with this. Ran out of the 1 million context window as LLM tried to finally
load all features on account of dependencies (references it encountered e.g. operate
calls, and different features referencing present one) - Cut up the set of features into a number of batches, a file every with 100s of
features, after which use LLM to investigate every batch in isolation. We confronted so much
of hallucination points, and file measurement points whereas streaming to mannequin. A number of
features had been transformed meaningfully however plenty of different features did not make
any-sense in any respect, all seemed like related capabilities, on cross checking we
realised the hallucination impact. - The subsequent try was to transform the features one after the other, to
guarantee LLM is supplied with a contemporary slender window of context to restrict
hallucination. We confronted a number of challenges (API utilization restrict, fee
limits) – We could not confirm what LLM translation of enterprise logic
was proper or mistaken. Then we could not join the dots between these
features. Attention-grabbing observe, we even discovered some C++ STDLIB features
like
std::vector::insert
on this method. We discovered so much had been truly unwind features purely
used to name destructors when exception occurs (stack
unwinding)
destructors, catch block features. Clearly we would have liked to give attention to
enterprise logic and ignore the compiled library features, additionally combined
into the binary
After these makes an attempt we determined to alter our method to slice the DLL based mostly
on purposeful space/workflow quite than take into account the whole meeting code.
Discovering the related operate
The primary problem within the purposeful space / workflow method is to discover a
hyperlink or entry level among the many 1000s of features.
One of many out there choices was to rigorously take a look at the constants and
strings within the DLL. We used the historic context: late Nineteen Nineties or early 2000
widespread architectural sample adopted in that interval was to insert knowledge into
the DB: was to both “choose for insert” or “insert/replace dealt with by saved
process” or through ADO (which is an ORM). Curiously we discovered all of the
patterns in several elements of the system.
Our performance was about inserting or updating the DB on the finish of the
course of however we could not discover any insert or replace queries within the strings, no
saved process to carry out the operation both. For the performance we
had been on the lookout for, it occurred to really use a SELECT by means of SQL after which
up to date through ADO (activex knowledge object microsoft library).
We acquired our break based mostly on the desk identify talked about within the
strings/constants, and this led to discovering the operate which is utilizing that
SQL assertion. Preliminary take a look at that operate did not reveal a lot, it may very well be
in the identical purposeful space however a part of a unique workflow.
Constructing the related subtree
ASM code, and our disassembly software, gave us the operate name reference
knowledge, utilizing it we walked up the tree, assuming the assertion execution is one
of the leaf features, we navigated to the mum or dad which referred to as this to
perceive its context. At every step we transformed ASM into pseudo code to
construct context.
Earlier after we transformed ASM to pseudocode utilizing brute-force we could not
cross confirm whether it is true. This time we’re higher ready as a result of we all know
to anticipate what may very well be the potential issues that would occur earlier than a
sql execution. And use the context that we gathered from earlier steps.
We mapped out related features utilizing this name tree navigation, generally
we now have to keep away from mistaken paths. We realized about context poisoning in a tough
approach, in-advertely we handed what we had been on the lookout for into LLM. From that
second LLM began colouring its output focused in the direction of what we had been trying
for, main into mistaken paths and eroding belief. We needed to recreate a clear
room for AI to work in throughout this stage.
We acquired a excessive stage define of what the totally different features had been, and what
they may very well be doing. For a given work move, we narrowed down from 4000+
features to 40+ features to take care of.
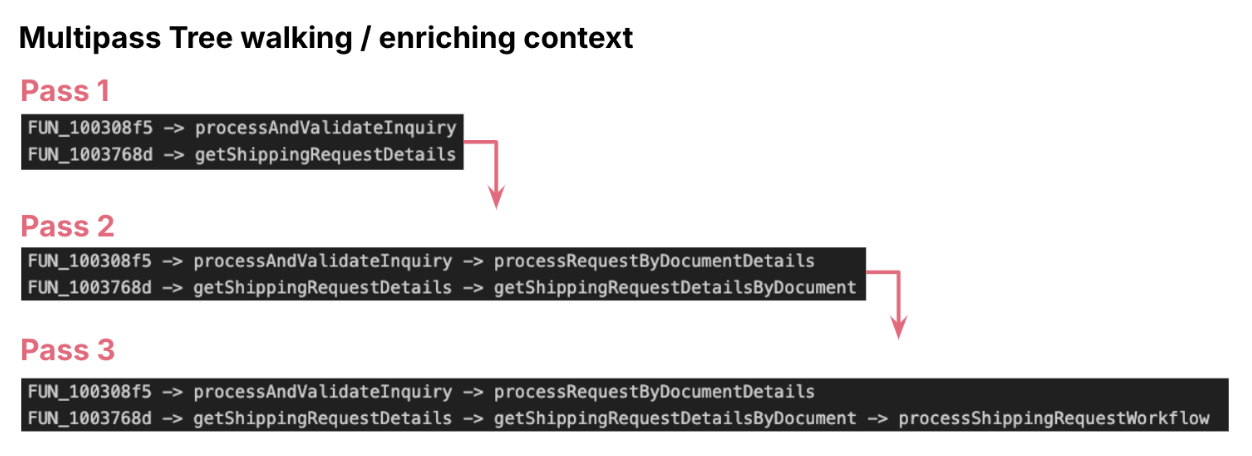
Multi-Go Enrichment
AI accelerated the meeting archaeology layer by layer, cross by cross: We
utilized multi cross enrichment. In every cross, we both navigated from leaf
node to prime of the tree or reverse, in every step we enriched the context of
the operate both utilizing its mother and father context or its little one context. This
helped us to alter the technical conversion of pseudocode right into a purposeful
specification. We adopted easy methods like asking LLM to offer
significant technique names based mostly on identified context. After a number of passes we construct
out your entire purposeful context.
Validating the entry level
The final and important problem was to substantiate the entry operate. Typical
to C++, digital features made it more durable to hyperlink entry features in school
definition. Whereas performance regarded full beginning with the foundation node,
we weren’t certain if there’s every other extra operation occurring in a
mum or dad operate or a wrapper. Life would have been simpler if we had debugger
enabled, a easy break level and assessment of the decision stack would have
confirmed it.
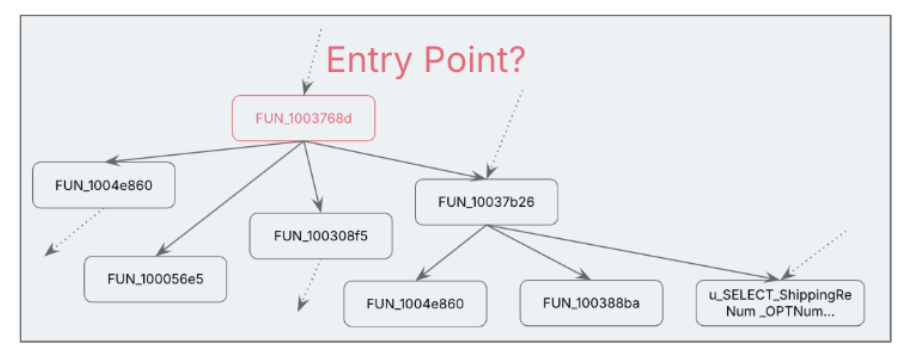
Nevertheless with triangulation methods, like:
- Name stack evaluation
- Validating argument signatures and the the return signature within the
stack - Cross-checking with UI layer calls (e.g., associating technique signature
with the “submit” name from Internet tier, checking parameter varieties and utilization, and
validating in opposition to that context)
Constructing the Spec from Fragments to Performance
By integrating the reconstructed components from the earlier levels:UI Layer
Reconstruction, Discovery with CDC, Server Logic Inference, and Binary
evaluation of App tier, an entire purposeful abstract of the system is recreated
with excessive confidence. This complete specification kinds a traceable and
dependable basis for enterprise assessment and modernization/ahead engineering
efforts.
From our work, a set of repeatable practices emerged. These aren’t
step-by-step recipes — each system is totally different — however guiding patterns that
form how you can method the unknown.
- Begin The place Visibility is Highest: Start with what you may see and belief:
screens, knowledge schemas, logs. These give a basis of observable habits
earlier than diving into opaque binaries. This avoids evaluation paralysis by anchoring
early progress in artifacts customers already perceive. - Enrich in Passes: Don’t overload AI or people with the entire system at
as soon as. Break artifacts into manageable chunks, extract partial insights, and
progressively construct context. This reduces hallucination threat, reduces
assumptions, scales higher with giant legacy estates. - Triangulate All the things: By no means depend on a single artifact. Affirm each
speculation throughout no less than two unbiased sources — e.g., a display move matched
in opposition to a saved process, then validated in a binary name tree. It creates
confidence in conclusions, exposes hidden contradictions. - Protect Lineage: Monitor the place each piece of inferred data comes
from — UI display, schema subject, binary operate. This “audit path” prevents
false assumptions from propagating unnoticed. When questions come up later, you
can hint again to authentic proof. - Preserve People within the Loop: AI can speed up evaluation, nevertheless it can’t
change area understanding. All the time pair AI hypotheses with skilled validation,
particularly for business-critical guidelines. Helps to keep away from embedding AI errors
straight into future modernization designs.
Conclusion and Key Takeaways
Blackbox reverse engineering, particularly when supercharged with AI, affords
vital benefits for legacy system modernization:
- Accelerated Understanding: AI accelerates legacy system understanding from
months to weeks, remodeling complicated duties like changing meeting code into
pseudocode and classifying features into enterprise or utility classes. - Lowered Concern of Undocumented Methods: organizations not must
worry undocumented legacy programs. - Dependable First Step for Modernization: reverse engineering turns into a
dependable and accountable first step towards modernization.
This method unlocks Clear Practical Specs even with out
supply code, Higher-Knowledgeable Choices for modernization and cloud
migration, Perception-Pushed Ahead Engineering whereas shifting away from
guesswork.
The long run holds a lot sooner legacy modernization because of the
impression of AI instruments, drastically decreasing steep prices and dangerous long-term
commitments. Modernization is anticipated to occur in “leaps and bounds”. Within the
subsequent 2-3 years we may count on extra programs to be retired than within the final 20
years. It is suggested to begin small, as even a sandboxed reverse
engineering effort can uncover shocking insights

