Your brokers are solely nearly as good because the information they will entry — and solely as secure because the permissions they implement.
We’re launching ACL Hydration (entry management record hydration) to safe information workflows within the DataRobot Agent Workforce Platform: a unified framework for ingesting unstructured enterprise content material, preserving source-system entry controls, and implementing these permissions at question time — so your brokers retrieve the proper info for the proper consumer, each time.
The issue: enterprise information with out enterprise safety
Each group constructing agentic AI runs into the identical wall. Your brokers want entry to information locked inside SharePoint, Google Drive, Confluence, Jira, Slack, and dozens of different techniques. However connecting to these techniques is barely half the problem. The tougher drawback is making certain that when an agent retrieves a doc to reply a query, it respects the identical permissions that govern who can see that doc within the supply system.
Right now, most RAG implementations ignore this solely. Paperwork get chunked, embedded, and saved in a vector database with no file of who was — or wasn’t — imagined to entry them. This can lead to a system the place a junior analyst’s question surfaces board-level monetary paperwork, or the place a contractor’s agent retrieves HR recordsdata meant just for inner management. The problem isn’t simply the right way to propagate permissions from the information sources in the course of the inhabitants of the RAG system — these permissions must be repeatedly refreshed as individuals are added to or faraway from entry teams. That is essential to maintain synchronized controls over who can entry varied kinds of supply content material.
This isn’t a theoretical danger. It’s the rationale safety groups block GenAI rollouts, compliance officers hesitate to log off, and promising agent pilots stall earlier than reaching manufacturing. Enterprise clients have been specific: with out access-control-aware retrieval, agentic AI can’t transfer past sandboxed experiments.
Current options don’t clear up this nicely. Some can implement permissions — however solely inside their very own ecosystems. Others help connectors throughout platforms however lack native agent workflow integration. Vertical purposes are restricted to inner search with out platform extensibility. None of those choices give enterprises what they really want: a cross-platform, ACL-aware information layer purpose-built for agentic AI.
What DataRobot supplies
DataRobot’s safe information workflows present three foundational, interlinked capabilities within the Agent Workforce Platform for safe information and context administration.
1. Enterprise information connectors for unstructured content material
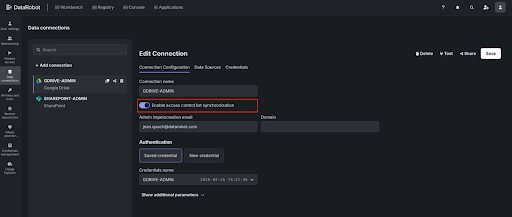
Connect with the techniques the place your group’s information truly lives. At launch, we’re offering production-grade connectors for SharePoint, Google Drive, Confluence, Jira, OneDrive, and Field — with Slack, GitHub, Salesforce, ServiceNow, Dropbox, Microsoft Groups, Gmail, and Outlook following in subsequent releases.
Every connector helps full historic backfill for preliminary ingestion and scheduled incremental syncs to maintain your vector databases present. You management entry and handle connections by APIs or the DataRobot UI.
These aren’t light-weight integrations. They’re constructed to deal with production-scale workloads — 100GB+ of unstructured information — with sturdy error dealing with, retries, and sync standing monitoring.
2. ACL Hydration and metadata preservation
That is the core differentiator. When DataRobot ingests paperwork from a supply system, it doesn’t simply extract content material — it captures and preserves the entry management metadata (ACLs) that outline who can see every doc. Consumer permissions, group memberships, position assignments — all of it’s propagated to the vector database lookup in order that retrieval is conscious of the permissioning on the information being retrieved.
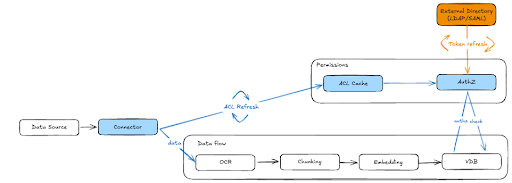
Right here’s the way it works (additionally illustrated in Determine 1 beneath):
- Throughout ingestion, document-level ACL metadata — together with consumer, group, and position permissions — is extracted from the supply system and persevered alongside the vectorized content material.
- ACLs are saved in a centralized cache, decoupled from the vector database itself. This can be a essential architectural determination: when permissions change within the supply system, we replace the ACL cache with out reindexing your entire VDB. Permission modifications propagate to all downstream shoppers routinely. This contains permissioning for regionally uploaded recordsdata, which respect DataRobot RBAC.
- Close to real-time ACL refresh retains the system in sync with supply permissions. DataRobot repeatedly polls and refreshes ACLs inside minutes. When somebody’s entry is revoked in SharePoint or a Google Drive folder is restructured, these modifications are mirrored in DataRobot on a scheduled foundation — making certain your brokers by no means serve stale permissions.
- Exterior identification decision maps customers and teams out of your enterprise listing (through LDAP/SAML) to the ACL metadata, so permission checks resolve appropriately no matter how identities are represented throughout totally different supply techniques.
3. Dynamic permission enforcement at question time
Storing ACLs is critical however not ample. The true work occurs at retrieval time.
When an agent queries the vector database on behalf of a consumer, DataRobot’s authorization layer evaluates the saved ACL metadata towards the requesting consumer’s identification, group memberships, and roles — in actual time. Solely embeddings the consumer is permitted to entry are returned. Every thing else is filtered earlier than it ever reaches the LLM.
This implies two customers can ask the identical agent the identical query and obtain totally different solutions — not as a result of the agent is inconsistent, however as a result of it’s appropriately scoping its information to what every consumer is permitted to see.
For paperwork ingested with out exterior ACLs (akin to regionally uploaded recordsdata), DataRobot’s inner authorization system (AuthZ) handles entry management, making certain constant permission enforcement no matter how content material enters the platform.
The way it works: step-by-step
Step 1: Join your information sources
Register your enterprise information sources in DataRobot. Authenticate through OAuth, SAML, or service accounts relying on the supply system. Configure what to ingest — particular folders, file varieties, metadata filters. DataRobot handles the preliminary backfill of historic content material.
Step 2: Ingest content material with ACL metadata
As paperwork are ingested, DataRobot extracts content material for chunking and embedding whereas concurrently capturing document-level ACL metadata from the supply system. This metadata — together with consumer permissions, group memberships, and position assignments — is saved in a centralized ACL cache.
The content material flows by the usual RAG pipeline: OCR (if wanted), chunking, embedding, and storage in your vector database of selection — whether or not DataRobot’s built-in FAISS-based answer or your individual Elastic, Pinecone, or Milvus occasion — with the ACLs following the information all through the workflow.
Step 3: Map exterior identities
DataRobot resolves consumer and group info. This mapping ensures that ACL permissions from supply techniques — which can use totally different identification representations — will be precisely evaluated towards the consumer making a question.
Group memberships, together with exterior teams like Google Teams, are resolved and cached to help quick permission checks at retrieval time.
Step 4: Question with permission enforcement
When an agent or software queries the vector database, DataRobot’s AuthZ layer intercepts the request and evaluates it towards the ACL cache. The system checks the requesting consumer’s identification and group memberships towards the saved permissions for every candidate embedding.
Solely approved content material is returned to the LLM for response era. Unauthorized embeddings are filtered silently — the agent responds as if the restricted content material doesn’t exist, stopping any info leakage.
Step 5: Monitor, audit, and govern
Each connector change, sync occasion, and ACL modification is logged for auditability. Directors can observe who linked which information sources, what information was ingested, and what permissions have been utilized — offering full information lineage and compliance traceability.
Permission modifications in supply techniques are propagated by scheduled ACL refreshes, and all downstream shoppers — throughout all VDBs constructed from that supply — are routinely up to date.
Why this issues to your brokers
Safe information workflows change what’s attainable with agentic AI within the enterprise.
Brokers get the context they want with out compromising safety. By propagating ACLs, brokers have the context info they should get the job completed, whereas making certain the information accessed by brokers and finish customers honors the authentication and authorization privileges maintained within the enterprise. An agent doesn’t grow to be a backdoor to enterprise info — whereas nonetheless having all of the enterprise context wanted to do its job.
Safety groups can approve manufacturing deployments. With source-system permissions enforced end-to-end, the chance of unauthorized information publicity by GenAI isn’t simply mitigated — it’s eradicated. Each retrieval respects the identical entry boundaries that govern the supply system.
Builders can transfer sooner. As an alternative of constructing customized permission logic for each information supply, builders get ACL-aware retrieval out of the field. Join a supply, ingest the content material, and the permissions include it. This removes weeks of customized safety engineering from each agent venture.
Finish customers can belief the system. When customers know that the agent solely surfaces info they’re approved to see, adoption accelerates. Belief isn’t a function you bolt on — it’s the results of an structure that enforces permissions by design.
Get began
Safe information workflows can be found now within the DataRobot Agent Workforce Platform. If you happen to’re constructing brokers that must purpose over enterprise information — and also you want these brokers to respect who can see what — that is the potential that makes it attainable. Attempt DataRobot or request a demo.

