
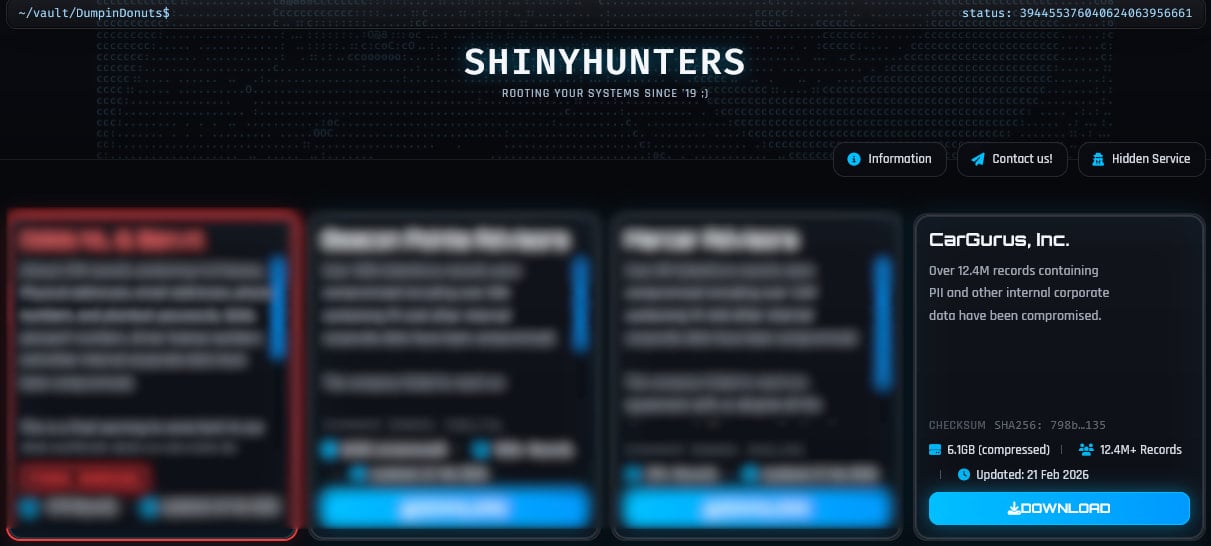
The ShinyHunters extortion group has printed private data in additional than 12 million data allegedly stolen from CarGurus, a U.S.-based digital auto platform.
CarGurus is a publicly traded automotive analysis and buying firm that operates within the U.S., Canada, and the U.Ok. Its web site has an estimated 40 million month-to-month guests and helps folks discover, evaluate, and make contact with sellers of latest and used autos.
On February 21, the menace group printed a 6.1GB archive containing 12.4 million data, saying it was from CarGurus. A day later, the HaveIBeenPwned (HIBP) information breach monitoring and alerting platform added the dataset, itemizing the next information varieties as compromised:
- Electronic mail addresses
- IP addresses
- Full names
- Telephone numbers
- Bodily addresses
- Person account IDs
- Finance pre-qualification utility information
- Finance utility outcomes
- Vendor account particulars
- Subscription data
Though CarGurus has not launched an official assertion disclosing a knowledge breach and didn’t reply to BleepingComputer’s request for remark, you will need to observe that HIBP makes an attempt to verify the validity/authenticity of the leaked data earlier than including them.
HIBP reviews that 70% of the leaked information was already on its database from earlier incidents, so roughly 3.7 million data are contemporary. Because the data is freely accessible for obtain, cybercriminals might reap the benefits of it for phishing assaults.
Supply: BleepingComputer
CarGurus customers are suggested to remain alert for probably malicious communications and rip-off makes an attempt leveraging the leaked data.
The ShinyHunters information extortion group has been very lively lately, claiming a number of assaults on giant firms and leaking their information when negotiations reached a useless finish.
The latest examples embody Dutch telecommunications supplier Odido, advert tech agency Optimizely, fintech agency Determine, outerwear model Canada Goose, restaurant chain Panera Bread, on-line courting firm Match Group, and music streaming platform SoundCloud.
The menace group usually makes use of social engineering, mostly voice phishing, to breach organizations, directing victims to credential-harvesting pages that grant them entry to SaaS platforms equivalent to Salesforce, Okta, and Microsoft 365.
Earlier ShinyHunters campaigns additionally concerned tricking staff into putting in malicious OAuth functions that granted them API-level learn entry to buyer information tables inside Salesforce cases.
Fashionable IT infrastructure strikes sooner than handbook workflows can deal with.
On this new Tines information, learn the way your staff can cut back hidden handbook delays, enhance reliability via automated response, and construct and scale clever workflows on prime of instruments you already use.



